Ssh
Connect to remote host with ssh keys
On the client
Prepare folder (if needed)
$mkdir ~/.ssh
$chmod 700 ~/.ssh
$cd ~/.sshCreate a ssh key (if you don't have one !)
$ssh-keygen -t rsa -C "id_rsa"Copy your pub certificate to remote
$scp -p id_rsa.pub remoteuser@remotehostOn the remote (server/client)
Connect to your remote server/client
$ssh remoteuser@remotehostPrepare folder
$mkdir ~/.ssh
$chmod 700 ~/.sshCopy the key into a authorized file
IMPORTANT : You need to edit the authorized_keys on the right user, if you need to allow multiple user, you need to edit all “.ssh\authorized_keys” under all users !!
$touch ~/.ssh/authorized_keys
$cat id_rsa.pub >> ~/.ssh/authorized_keys
$chmod 600 ~/.ssh/authorized_keysRemove password authentication and allow ssh connect RSA
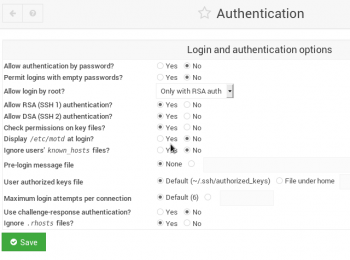
Here i use webmin
Connect with public key
$chmod -R 600(or 700 ?) id_rsa.priv.txt
$ssh -i id_rsa.priv root@IPSource : sourceforge
Date : 2018.06.15
Regenerate ssh key
Delete old keys
$/bin/rm -v /etc/ssh/ssh_host_*Reconfigure openssh-server
$dpkg-reconfigure openssh-serverRestart the service
$systemctl restart sshUpdate your client with new key
$ssh-keygen -R IP_of_your_serverChange ssh banner
Change the prompt
$nano /etc/issueChange banner when logon
$nano /etc/motdEdit the "etc/issue"
How to
$nano etc/issueescape sequences : \b -- Baudrate of the current line. \d -- Current date. \s -- System name, the name of the operating system. \l -- Name of the current tty line. \m -- Architecture identifier of the machine, eg. i486 \n -- Nodename of the machine, also known as the hostname. \o -- Domainname of the machine. \r -- Release number of the OS, eg. 1.1.9. \t -- Current time. \u -- Number of current users logged in. \U -- The string "1 user" or " users" where is the number of current users logged in. \v -- Version of the OS, eg. the build-date etc.
For example :
If “/etc/issue” file contain “Debian GNU/Linux \d”
Output look like :
Debian GNU/Linux Web Feb 22 2017Source : cyberciti